EndPoint Security: how does it prevent data theft? | KnowledgeNile
Data thefts in professional workplaces frequently happen although a significant number of them stay unnoticed for quite a while. Medium and small companies are usually the most severely influenced, particularly when no security estimations are set up inside the IT frame. Endpoint security programming does not just ensure and shield business insider facts, financial assets and significant resources, they also effectively avoid extreme harm to the organization’s status which might be demolished where secret organization data can be leaked.
What Is Endpoint Security or Endpoint Protection and why is It Important?
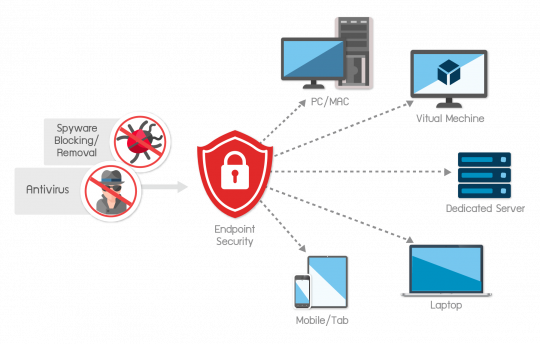
Endpoint security alludes to safeguarding endpoints, or user devices like workstations, desktops, laptops and mobile phones. Endpoint security programming shields these purposes of passage from unsafe action as well as a serious outbreak. At the point when organizations can guarantee endpoint amenability with information security gauges, they can keep up more prominent command over the developing number and sort of entrance points to the system.
Endpoint Security or endpoint protection is regularly mistaken for various other system security devices like firewall, antivirus and network security.
Source- uih
How Endpoint Security prevents data theft
Security from Theft
There are various security ways to shield your information from aggressors striving to get in, yet none can help if your devices are physically misplaced. This is the place where endpoint security tools are required. Endpoint protection utilizes a ready passcode to secure a machine, so nothing on the device can boot-up until the right code is entered.
Assist system
An endpoint security protections would help a framework manager, and users access rights, to effectively control the entrance of convenient tools and to observe and distinguish peculiarities and actions in the corporate system, for example, an employee endeavoring to duplicate confidential business data onto a USB.
Controlling unknown devices
A perfect endpoint security tools offer the capacity to examine for new obscure devices and to supervise them in a concentrated device databank, as well as the ability to regulate and promptly close a moveable device retrieved on a client machine which is incidentally disconnected and isn’t an associate from the company network.

Comments
Post a Comment